
The internet has made it easier than ever before to operate and manage industries. Companies are using new technology to remotely access industrial networks and make real time changes. Even vendors are using the internet in new ways, creating apps for constant communication.
Access to information has never been greater with untold amounts of real-time data being collected across industries. This much new access and new data has created a need for increased cyber security. The fundamental fact that every system has vulnerabilities threatens interconnectivity and advancement of businesses.
There is an inherent risk that all data can be hacked — but by taking the necessary precautions this risk can be minimized.
Layered Security
The first step is to create a layered security system. Security measures have gaps and to cover these gaps you’ll need to use unique security measures. Consult with your I.T. department and find out what tools they’re using and what you should add. The more diverse your security solution the less potential gaps you’ll have.
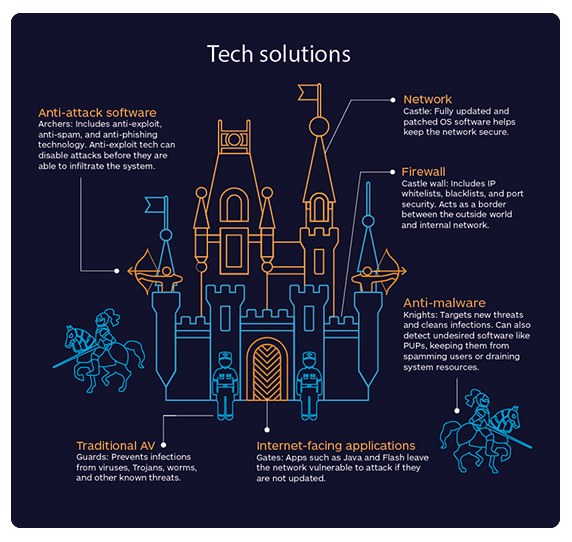
What Layered Security Isn’t
Layered security is not the redundant use of one of the same tools. Two anti-virus scanners are not necessarily better than one. Layered security is about multiple tools each protecting you from a different variety of potential breaches.
The Defense-in-Depth Strategy
Defense-in-Depth assumes someone will try to get into your system and they will at least partially succeed. Defense-in-Depth uses the tools of layered security, but applies them on a much wider scale. The goal is to secure all parts of your system and property. When someone gets into a layer of your system the other layers will prevent the breach from spreading or at least slow down unauthorized access until it can be detected. Some of these layers include:
Security Policies
Security polic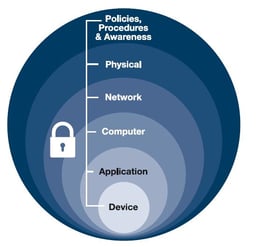 ies control how effective the practises you implement will be. They are the rules for how each security measure should be used. Password policy will dictate how strong employee’s passwords should be and when they should be changed. The creation of policy isn’t enough. It is necessary to monitor their usage so that they can improve over time. Each additional policy you create and enforce will eliminate more chances of accidental and preventable security risks.
ies control how effective the practises you implement will be. They are the rules for how each security measure should be used. Password policy will dictate how strong employee’s passwords should be and when they should be changed. The creation of policy isn’t enough. It is necessary to monitor their usage so that they can improve over time. Each additional policy you create and enforce will eliminate more chances of accidental and preventable security risks.
Be Better than Average
The average business is vulnerable to some type of network attack. By keeping the above strategies and policies in mind you’ll keep your business safer. To get you started I’ve listed a few specific examples that can help.
Update Everything
Make sure all of your software and firmware is constantly updated. Remember you’re not the only one invested in your security. Distributors and manufacturers do not want to see their hardware exploited and can help you keep up to date. Ask them for ways you can help keep your systems secure and your data private.
Encrypt Everything
Encryption is one of the easiest and most powerful tools you can use. It can be implemented on all levels of your network. Remote industrial networking devices should use network protocols like VPN (Virtual Private Network) and SSL (Secure Sockets Layer), while local data should be encrypted using a hardware or software algorithm.
Conclusion
The newest networking trends such as the Industrial Internet of Things (IIoT), Big Data, etc. all revolve around the internet. To protect and secure your business and customer information it is necessary to address your network security.
Modern data security doesn't just protect your company’s financial and personal interests—it also protects the business's reputation. Nothing looks worse for a modern company than a data break of any sort. These problems can alienate existing customers, dissuade potential customers, and even disqualify you from certain government work.
So take a long look at your current security measures and see if they are ways you can apply the above strategies to keep your network and your interests secure. Finally, don’t be afraid to ask for our help in any of your networking needs because our focus is simple… the success of our customers.


