 The increased interconnection of industrial assets has certainly given way to greater productivity, reliability and flexibility within the marketplace, but it has also brought along cyber-espionage. The use of ethernet connections is only bound to increase as more industries embrace greater automation. The increased need for sharing data, both from machine-to-human as well as machine-to-machine has made industrial networks open ended. This makes them prone to major attacks that can greatly effect production and lead to safety risks at sensitive installations.
The increased interconnection of industrial assets has certainly given way to greater productivity, reliability and flexibility within the marketplace, but it has also brought along cyber-espionage. The use of ethernet connections is only bound to increase as more industries embrace greater automation. The increased need for sharing data, both from machine-to-human as well as machine-to-machine has made industrial networks open ended. This makes them prone to major attacks that can greatly effect production and lead to safety risks at sensitive installations.
The threats that modern industrial networks face:
This is just a glimpse of what waits for an industrial network from the other side. Therefore, the need for a comprehensive protection mechanism is very real, in order to ensure continuous operations and safety of assets in sensitive industrial sectors.
Every module has a backdoor, an opening, or a breaking limit. An optimum industrial security solution would be one that takes into account the current threats as well as adapts to the oncoming ones. This can only be done through constant collaboration and upgradation of resources, something Siemens is offering.
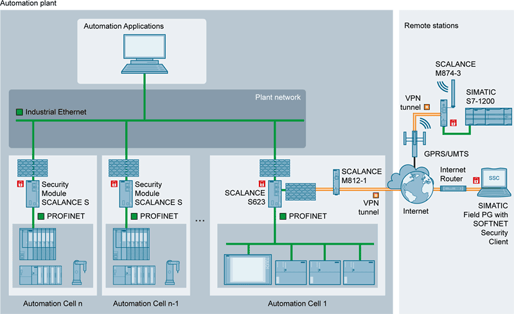
Siemens offers a multi-level security concept that covers the entire plant and provides in-depth protection. The core of this security infrastructure sits on top of network security and system integrity, to ensure non-stop operation of assets even in the case of an attack.
 The SCALANCE S modules are the perfect instantiation of Siemen’s integrated security. The security modules of SCALANCE S range are widely used to protect against ethernet based intrusions. Data transmission between devices is encrypted and protected against tampering of any kind, while allowing remote connections via internet for data sharing and control.
The SCALANCE S modules are the perfect instantiation of Siemen’s integrated security. The security modules of SCALANCE S range are widely used to protect against ethernet based intrusions. Data transmission between devices is encrypted and protected against tampering of any kind, while allowing remote connections via internet for data sharing and control.
At a glance, SCALANCE provides:
SCALANCE S is designed to be used in automation-rich industrial environments, meeting all the specific requirements for such a setup. There are 4 product versions of the SCALANCE S, namely the S602, S612, S623 and S627-2M.
The S627-M is the most comprehensive solution for ensuring top of the line protection from any network-oriented threats.
The S627-M features include:
VPN
Limited to S612, S623 and S627-2M, Virtual Private Networks are available for guaranteeing secure communications, reliable authentication and data integrity.
All incoming traffic is first monitored, and filtered thoroughly for any discrepancies. There is a constant threat to industrial ethernet networks from falsified IP addresses, therefore the SCALANCE S performs authentication through VPN mechanisms. From thereon, data communication takes place within a secure “tunnel”, protecting it from espionage and manipulation.
Firewalls
Acts as a supplementary function to VPNs, and provides flexible access control for data packets coming from internal or external sources. The firewall filters data packets, keeping the system isolated from any unauthorized source of communication. Furthermore, a constant log is maintained to allow backtracking in case of any suspicious event.
Configuration
The Security Configuration Tool is used to carry out central configuration of all SIMATIC NET security products. The configuration specifications may be stored within a C-PLUG swap media to allow easy implementation in case of a fault.
As a whole, Siemens security products offer unparalleled protection against all threats, ranging from those that put industrial assets out of order to those that put the lives of workers at risk. Continuity of operations is vital in case of industrial connections, as even a single interruption can have a cascade effect on the workings of the entire network.
Interested in learning more about Siemens security products?
You may also be interested in reading:


